DORA First Anniversary: Sixteen Months In, EU Banks Have Learned the Cost of Cyber Resilience
Sixteen months after the Digital Operational Resilience Act (DORA) entered full application in January 2025, the EU’s banking sector has lived through its first full cycle of compliance, supervision and incident reporting under the new framework. With the European Banking Authority preparing its first horizontal review for the second half of 2026, a clearer picture is emerging of what DORA has actually changed — and what remains contested.
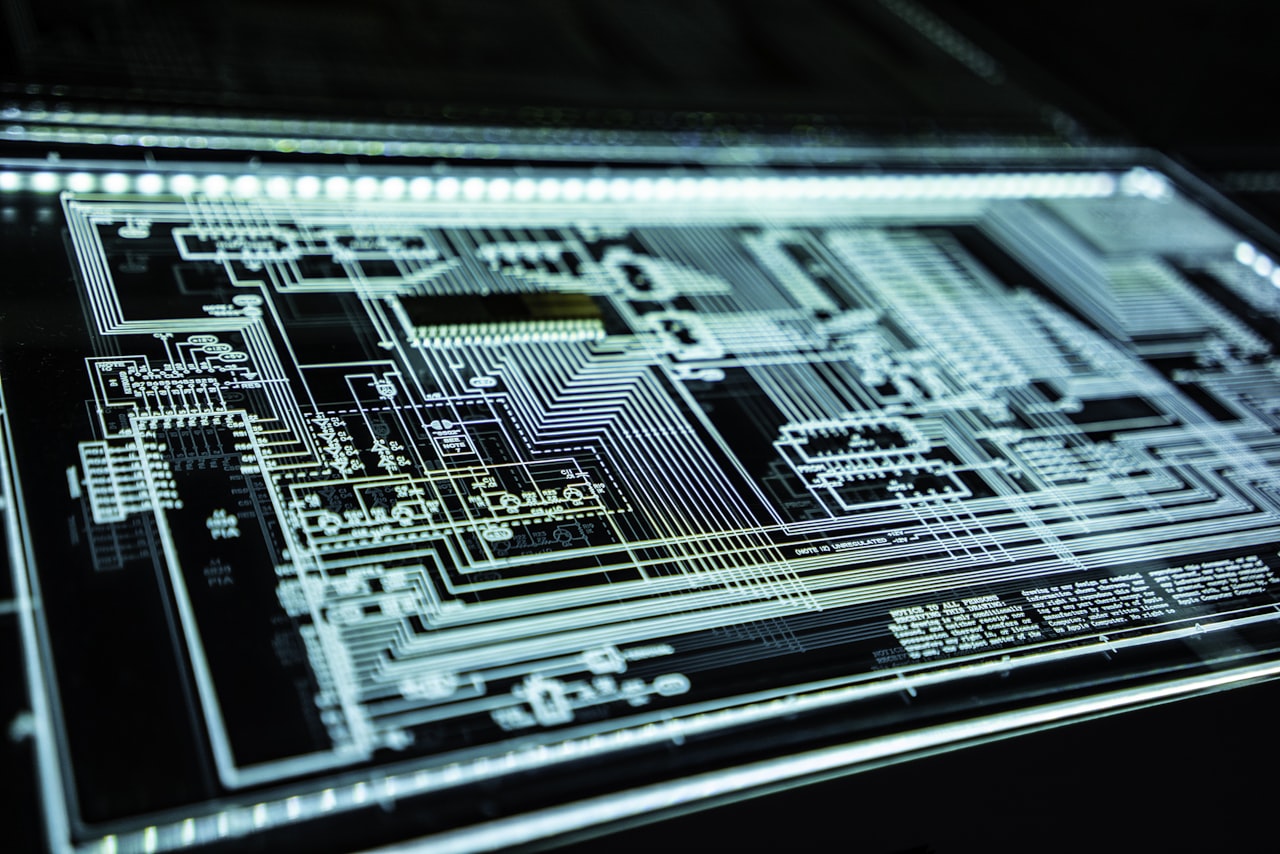
What DORA actually requires
DORA applies to over 22,000 financial entities across the EU — banks, insurers, investment firms, crypto-asset service providers, and certain critical ICT third-party service providers. The core obligations sit in five pillars: ICT risk management, ICT-related incident reporting, digital operational resilience testing, third-party risk management, and information sharing. The threshold for major incident reporting is calibrated against impact metrics; the testing obligations include threat-led penetration testing for systemically important entities every three years.
The first-year experience
The first-year experience has been uneven. Large incumbent banks with mature cyber security functions absorbed DORA’s requirements with relative ease — the framework codified what was already best practice in those institutions. Mid-size and challenger banks, by contrast, faced more substantial gap-closing programmes, particularly on third-party risk management where the documentation requirements are intensive. Crypto-asset service providers, brought into the regulated perimeter for the first time by DORA in conjunction with MiCA, have struggled most — many were operating with operational resilience postures designed for early-stage technology rather than regulated finance.
The third-party question
The most operationally significant DORA chapter has proven to be third-party risk management. EU financial institutions have collectively renegotiated thousands of contracts with major ICT providers — Microsoft Azure, Amazon Web Services, Google Cloud, Salesforce, ServiceNow, and the major core banking software vendors. The renegotiations have focused on audit rights, sub-contracting transparency, exit rights, and concentration risk. The European Supervisory Authorities (ESAs) have published the first list of critical ICT third-party service providers, who will be subject to direct EU supervision — a regulatory innovation that goes well beyond historical precedent.
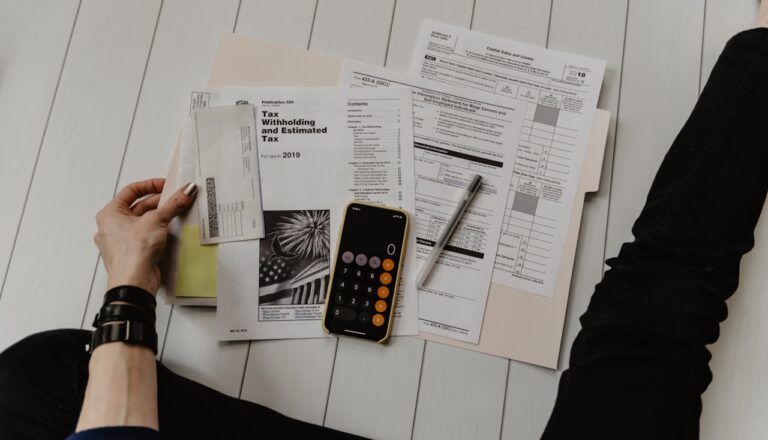
Incident reporting in practice
The incident reporting architecture has produced a steady flow of major incidents reported to national competent authorities and forwarded to the ESAs. The first year’s data — to be analysed in detail in the Banking Authority’s horizontal review — already shows two patterns: a high concentration of major incidents at a relatively small number of entities (suggesting maturity differences across the sector) and a clear correlation between severity and reliance on a small number of cloud providers. The latter finding is fuelling the broader debate on cloud concentration risk.
The intersection with the AI Act
DORA’s third-party risk management framework increasingly intersects with the AI Act’s high-risk AI obligations. Where a bank uses an AI-driven credit-scoring system from a third-party provider, the bank must comply with both DORA’s contractual and operational requirements and (from August 2026 or December 2027 depending on the Omnibus outcome) the AI Act’s high-risk obligations. The European Banking Authority and the EU AI Office are working on coordinated guidance to avoid compliance duplication, but the operational complexity remains real.
What the horizontal review will say
The Banking Authority’s first horizontal review, expected in the second half of 2026, will provide the first authoritative cross-EU assessment of DORA implementation. Areas likely to feature prominently include the calibration of major incident reporting thresholds (currently triggering more reports than supervisors can usefully process), the practical interpretation of threat-led penetration testing requirements, and the supervisory architecture for critical ICT third-party providers. The review will also feed into the broader policy debate on whether DORA-style operational resilience obligations should be extended to other regulated sectors — an idea floated by some Commission officials in early 2026.